
Promotion Across Kubernetes and Hybrid Environments
In 2026, multi- and hybrid environments are increasingly the norm. For platform engineering, DevOps and application developers, this adds complexity t...

In 2026, multi- and hybrid environments are increasingly the norm. For platform engineering, DevOps and application developers, this adds complexity t...
Sidecarless service mesh architectures like Istio Ambient Mode are reducing complexity and reigniting enterprise adoption in 2026. The post Why Servic...

Ingress NGINX reached end-of-life in March 2026. Explore four migration strategies—alternate controllers, forks, direct Gateway API migration, and dua...

Kubernetes is the OS for modern apps — but enterprises need platforms, not just clusters. Focus on standardized paved paths, supply‑chain security (si...
Kubernetes is the default control plane for infrastructure but poses challenges for developers managing its complexities. Internal developer platforms...

In the cloud-native landscape, GitOps leads the way for continuous delivery, yet relying solely on synchronization can mask systemic issues. This arti...

In a recent talk, the disparity between developers and platform engineers in container security was highlighted, revealing how a single line of code c...
At the center of the dispute is how far AI models should be allowed to go inside military systems.
Google has patched 129 Android vulnerabilities, including an actively exploited flaw in a widely used Qualcomm component.
Researchers have found that attackers are abusing OAuth to send users from legitimate Microsoft or Google login pages to phishing sites or malware dow...
Reports of a "Great British Firewall" are exaggerated. And even if they wanted to, here's why it would be virtually impossible.
Google has urged the justices to strike down the controversial warrants, which can sweep up location data from hundreds of phones near a crime scene.

We uncovered a fake CleanMyMac site delivering SHub Stealer, a macOS infostealer that steals credentials and silently backdoors crypto wallets.
Bing search results pointed victims to GitHub repositories claiming to host OpenClaw installers, but in reality they installed malware.
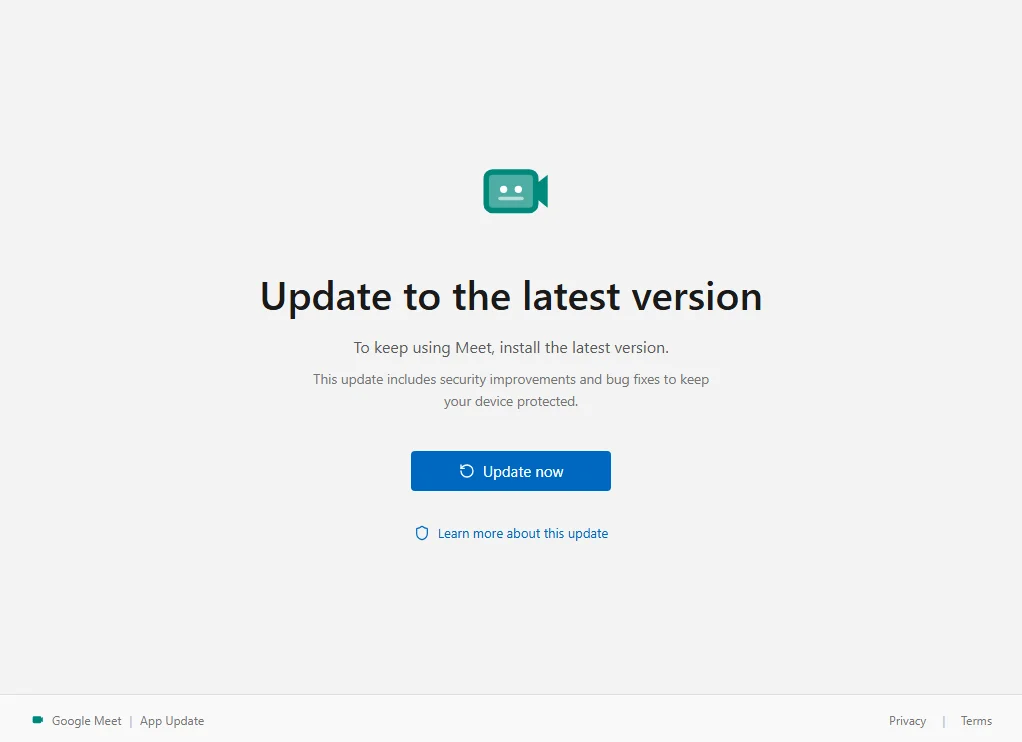
We found a fake Google Meet update that enrolls the victim's Windows PC in an attacker's device management system.
Researchers uncovered fake Claude Code install pages spreading infostealers that steal passwords and browser sessions.
A suspected breach of the FBI’s wiretap network has investigators asking whether a nation-state was involved.
Dutch intelligence warns that attackers are hijacking Signal and WhatsApp accounts by tricking users into sharing verification codes or linking a mali...
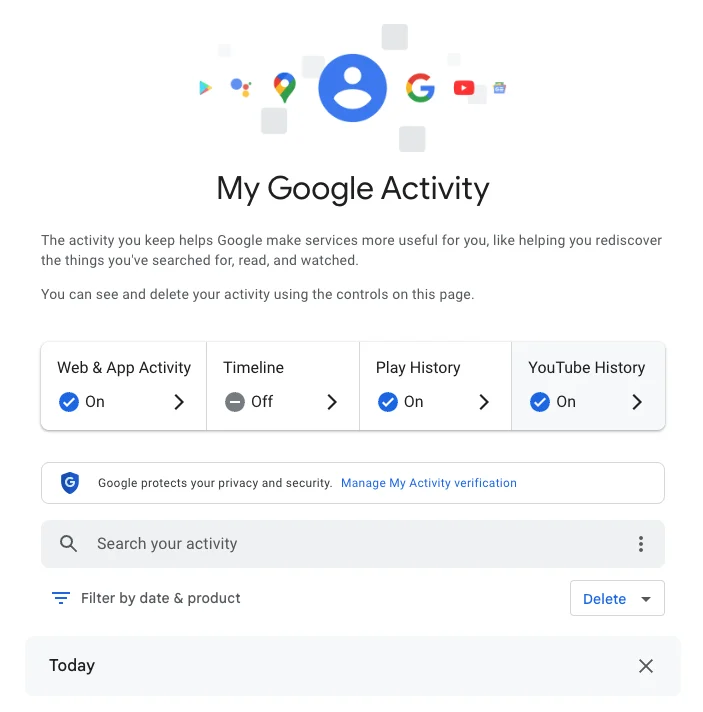
Google knows a lot about you. Here's how to check your Google Search history and how to prevent future tracking.
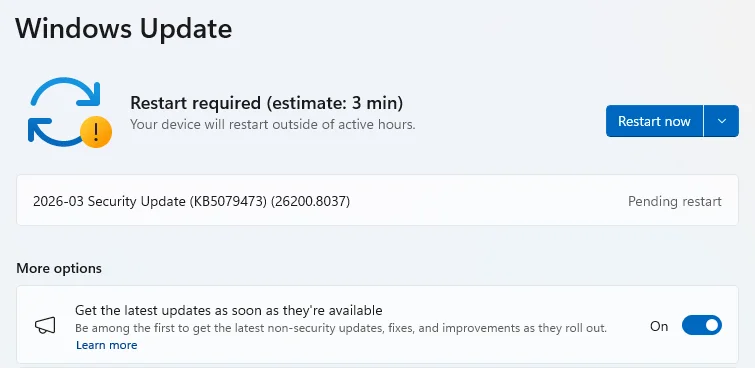
Microsoft patched 79 security vulnerabilities this month, including bugs that could let attackers escalate privileges or crash critical services.